A lawyer was working late one night when he saw a colleague’s computer suddenly turn on. Files flashed up on the screen as though someone were at the empty desk searching through the firm’s documents and data.
Get Instant Access to This Article
Subscribe to Worcester Business Journal and get immediate access to all of our subscriber-only content and much more.
- Critical Central Massachusetts business news updated daily.
- Immediate access to all subscriber-only content on our website.
- Bi-weekly print or digital editions of our award-winning publication.
- Special bonus issues like the WBJ Book of Lists.
- Exclusive ticket prize draws for our in-person events.
Click here to purchase a paywall bypass link for this article.
A lawyer was working late one night when he saw a colleague’s computer suddenly turn on. Files flashed up on the screen as though someone were at the empty desk searching through the firm’s documents and data.
Michelle Drolet, CEO of Framingham-based cybersecurity company Towerwall Inc., said the company was one of a number of small law firms hit by a type of phishing scam. The perpetrators had claimed to be part of a managed service provider and convinced an employee to provide a password and download software onto the computer.

“In this case, they sat there dormant until the nighttime, and then they started to find a lot of stuff,” Drolet said.
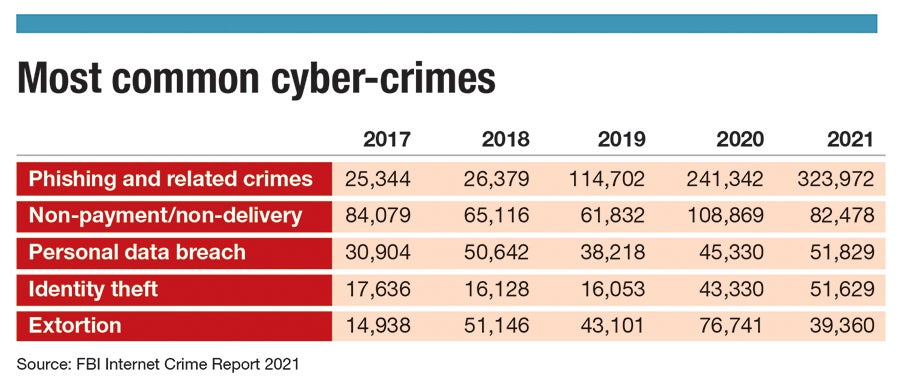
Cyberattacks like this are part of a growing trend, Drolet and others from the industry in Central Massachusetts said. They pointed to a number of trends leading to increased cybercrime, making small companies especially vulnerable.
“Often, small under-resourced firms that don’t have IT departments don’t devote a lot of attention to this,” said Stephanie Helm, director of the MassCyberCenter at the MassTech Collaborative in Westborough. “A lot of them just don’t view this as a threat to them ‘Because I’m small potatoes.’”

But Helm said it’s becoming easier for bad actors to find vulnerable targets in an almost automated fashion. For example, bots can scour Microsoft Exchange email servers, looking for users who had failed to patch their systems after a vulnerability was discovered.
“It’s not personal,” Helm said. “That bot doesn’t know who you are. They just know you’re an easy target.”
More sophisticated attacks
One way cybercriminals can exploit a company once they’re inside the system is ransomware. This technique has become more sophisticated over time, Helm said. A few years ago, criminals would simply freeze a company’s data and make it pay to get it back. Companies could protect themselves against this threat simply by keeping everything securely backed up. But today, hackers are more likely to spend time learning about the company’s operation and seeking out sensitive information like customer data they can threaten to sell on the dark web if a company doesn’t pay up.
“They have gotten very organized, and they have become like corporations of bad guys,” Helm said. “They’ve got parts of the company that specialize in establishing access to networks, parts that are really good at negotiations. Some specialize in healthcare organizations, some in financial organizations. They’ve got guys that specialize in moving the money after they get paid so that nobody finds out and traces it back to them.”
In some cases, she said, the criminals are operating in countries that can’t or won’t stop them, or even nations like North Korea where the government may view cybercrime as a useful revenue stream.
The threat has gotten much more serious, with typical ransoms rising from around $1,000 to more than $1 million, Drolet said. And, just as significantly, companies may have to pause operations while they deal with the frozen data, potentially harming their customer relationships and reputation.
“If [a small or midsize business] is hit with ransomware, it’s typically out of business within six months,” she said.
Fixing the weakest links
While installing software patches and maintaining best practices with firewalls and anti-virus programs is important, several tech professionals said the biggest key to staying safe is employee training.
“Unfortunately, the weakest link in cybersecurity is us, the end user,” said Libis Bueno, CEO of the Worcester IT and cybersecurity firm Domitek.

For example, Bueno said sales people are often eager to respond to emails right away in the hopes of winning a new client. But, if they’re not alert to danger, this can cause them to click on unsafe links or provide information opening up new vulnerabilities.
Another common scam is when a person will contact the human resources department posing as an employee and ask to change their direct deposit information, sending their salaries to an account owned by the scammer, said Helder Machado, CEO of Machado Consulting Inc. in Worcester. When this happens, Machado said, there’s no way to get the money back.

“It’s gone,” he said. “That money’s gone. It hits that account, and it moves right out.”
To avoid this situation, he said, companies need a policy in place requiring they call an employee or vendor to confirm any financial change.
Companies' vulnerabilities grew when many people began working from home in 2020, Bueno said. If a worker’s child downloads a game on their laptop, it may bring infected code with it. Then, when the worker connects to the company’s virtual private network, it can spread.
“VPN is just a tunnel from your computer to the office, so you just opened that door,” Bueno said.
Preventing & preparing for attacks
Companies sometimes assume if they have cyber insurance, any losses they incur from hacking will be covered, but that’s not always the case. If a client isn’t doing its part to keep its systems safe, insurance may not cover a claim, Machado said.
It’s now more difficult to get insured in the first place, Drolet said.
“People are losing cyber insurance, or premiums are going up 50% to 100%,” she said.
To qualify for insurance, companies may have to show they’re doing everything they can to reduce their vulnerability. One key is simply to have a plan in place for what to do if the company is attacked, Helm said.
“Think about what would happen if you woke up one day and it had happened,” she said “What would you do?”
If a company doesn’t have a relationship with an IT firm, it may waste valuable time trying to find one to help in an emergency. In general, Helm said, it’s best to have an ongoing relationship with someone who understands cybersecurity, whether it’s an employee, a company hired on retainer, or even a particularly helpful and tech-savvy friend. On the whole, she said, a company without its own IT department can usually benefit from working with a firm to help with training staff and staying apprised of best security practices.
“It’s really important that you find good companies, good partnerships to help you,” Machado said. “Most small business owners, this is overwhelming. They’re busy running their own businesses.”

